The Gately Report: Emsisoft Analyst Shines Light on Clop Ransomware Gang's MOVEit Transfer Attacks
Plus, Vade discovers a new Microsoft 365 phishing attack that could impact business’ most sensitive data.

Already have an account?
It’s doubtful we’ll ever know the full extent of the Clop ransomware gang’s massive MOVEit Transfer attacks.
 That’s according to Brett Callow, ransomware expert and threat analyst at Emsisoft. He’s been tracking the attacks since the start, including all of the organizations Clop has listed as victims.
That’s according to Brett Callow, ransomware expert and threat analyst at Emsisoft. He’s been tracking the attacks since the start, including all of the organizations Clop has listed as victims.
Emsisoft is a New Zealand-based endpoint protection company that makes antivirus and anti-malware solutions. It has reseller and MSP partners across the globe.
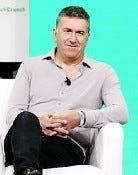
Emsisoft’s Brett Callow
“My research highlights the direction the threat landscape is taking,” Callow said. “And obviously we have to fine-tune our products to take account of that. Threats aren’t the same all the time. Defenses can’t be the same all the time either.”
Clop Ransomware Gang Victims Increasing Daily
The number of MOVEit Transfer attack victims grows by the day. The Clop ransomware gang claims to have stolen data from hundreds of MOVEit Transfer users, and at least 200 organizations have been identified, ranging from U.S. government agencies, to the California Public Employees’ Retirement System (CalPER) and the California State Teachers Retirement System (CalSTRS), EY, Shell and Cadence Bank.
The number of individuals whose personal information was compromised now exceeds 17.5 million.
Callow said the extent and the scope of this incident is “quite surprising.”
“We are potentially looking at hundreds of organizations here that have lost data, sometimes directly from their own MOVEit installations and sometimes indirectly through the MOVEit installations of their providers, service providers and business partners,” he said. “Clop has been releasing data in some of the cases. I’ve not accessed that data, so I can’t tell you how much of it there is or exactly what it is other than it’s there. And there is now a huge amount of information on that [Clop] site that can be accessed by other cybercriminals and used for their own nefarious purposes, but may also use some of the data that they have stolen for phishing schemes to lure in more victims.”
Scroll through our slideshow above for more from Callow and more cybersecurity news.
Want to contact the author directly about this story? Have ideas for a follow-up article? Email Edward Gately or connect with him on LinkedIn. |
About the Author
You May Also Like


